FBI Notification for Ransomware Attacks Against Casinos

According to a recent FBI notification, ransomware gangs’ infiltration of casinos is happening via third-party vendors. This week’s Private Industry Notification focuses on initial access methods prevalent as of July 2023.
Besides third-party vendors and services, threat actors have been eyeing legitimate system management tools to access and elevate system privileges. The FBI said that small and tribal casinos are mostly on ransomware gangs’ radar, with the end goal of encrypting servers and the personally identifying information (PII) of employees and customers.
“Attacks abusing Internet-accessible remote management portals has been a problem for decades, but it didn’t become a primary method of attack until the last few years,” Roger Grimes, Data-Driven Defense Evangelist at KnowBe4, told Spiceworks. “It went from being something that some criminals did some of the time to being a primary method used by many gangs.”
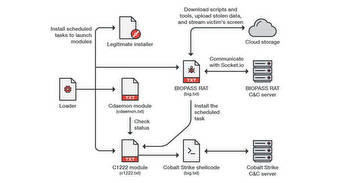
The FBI also highlighted the prevalence of the Silent Ransom Group (SRG) or Luna Moth, which carried out callback phishing data theft and extortion attacks. Threat actors tricked their targets into calling a designated number by enacting a ruse that they have pending charges on their accounts.
The actors then lead the target into setting up a legitimate system management tool via a link provided in a follow-up email. SRG would then use this tool to install other malware or repurpose it for malicious use to compromise local files and the shared network drives. The group engages in exfiltration and double extortion.
Palo Alto Networks’ Unit 42 explained, “By design, this style of social engineering attack leaves very few artifacts because of the use of legitimate trusted technology tools to carry out attacks. However, Unit 42 has identified several common indicators implying that these attacks are the product of a single highly organized campaign. This threat actor has significantly invested in call centers and infrastructure that’s unique to each victim.”
The FBI recommends maintaining offline backups of data, encryption of backups, reviewing the security posture of third-party vendors, implementing listing policies for applications and remote access policies, and monitoring external connections to mitigate the threat.
“If you’ve got a remote management access portal accessible from the Internet, it better be patched, require phishing-resistant MFA to access, VPN, or require a long, complex, and unique password. Else it’s likely to be discovered and hacked. When it’s a third party that has implemented the remote access portal, you…the primary customer, likely don’t even know about it, much less know to make sure it’s secured,” Grimes added.
How can organizations defend against ransomware? Please share with us on LinkedIn, X, or . We’d love to hear from you!